While anyone can use it, it’s built for high-stakes exchanges, making it overkill for routine file sharing or data backups. And it’s still essential to use strong passwords and two-factor authentication (2FA) to help keep your account secure. But while anonymous email services can help protect your identity, they don’t make you immune to threats like email spoofing or social engineering.
Accessing the dark web requires specialized software like Tor or I2P to bypass standard internet protocols and anonymize user activity. Trends indicate increased public curiosity about the dark web, often driven by media coverage of illicit marketplaces, hacking forums, or concerns over surveillance. However, legitimate research into dark web trends typically focuses on understanding anonymous communication, monitoring illegal activities (e.g., drug trafficking, cybercrime), or analyzing data for cybersecurity purposes. Researchers must navigate ethical and legal challenges, including ensuring compliance with data privacy laws and avoiding unintended exposure to harmful content.
Tor is the most popular way to access the dark web, but it’s not the only option. Most threats don’t come from the network itself — they come from the sites you visit, the files you download, and the mistakes you make. A VPN doesn’t encrypt traffic after it exits the Tor network. That means your ISP only sees encrypted VPN traffic and can’t tell you’re using Tor. Don’t download anything unless you’re absolutely sure it’s safe. Avoid fraudulent Tor-like browsers that compromise your online security.
The internet is a vast expanse of information, but not all of it is accessible through traditional search engines. Some areas are reserved for a select few, constituting what is commonly known as the dark web. Understanding how to access the dark web can be vital for various reasons, ranging from privacy to research. This article aims to shed light on the dark web, outlining safe practices and informing readers about the tools necessary for exploring its depths responsibly.
- It uses its own internal DNS to access “eepsites”, not .onion addresses.
- DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web.
- This process, known as “onion routing,” masks your IP address and encrypts your data, making it difficult for anyone to trace your online activity.
- Avoid changing default settings unless you know exactly what you’re doing.
- The dark web is a hidden part of the internet not indexed by regular search engines, accessed through specialized browsers like Tor.
What is the Dark Web?
The dark web is a subsection of the deep web, which comprises parts of the internet not indexed by standard search engines like Google. Unlike the surface web, which everyone uses daily, the dark web is often associated with anonymity and often houses various illicit activities. However, it also serves legitimate purposes, such as protecting users' privacy in oppressive regimes or fostering free speech.
Why Access the Dark Web?
There are several legitimate reasons to access the dark web. Journalists, researchers, and activists often use it as a means to communicate securely and access information without censorship. Additionally, individuals concerned about their privacy may seek the dark web to browse and share information without being tracked.
How to Access the Dark Web Safely
Accessing the dark web requires specific tools and precautions. Here’s a step-by-step guide:
1. Install a Secure Browser
The most common method to access the dark web is through the Tor browser, which anonymizes your internet traffic. Download the Tor browser from the official website to ensure you receive the latest version without malicious software.
2. Use a VPN
A Virtual Private Network (VPN) adds an additional layer of privacy. By routing your internet connection through a secure server, a VPN helps mask your IP address, making it harder to trace your online activities.
3. Stay Aware of Security Risks
- Combined with smart surfing behaviour and technologies like Tor and a VPN, even the darkest reaches of the internet may be securely traversed.
- Most internet users want to use the dark web safely, but it’s still important to be careful when using any onion browser.
- Keeping your security software up-to-date is vital in protecting your device from threats.
- Browsing the dark web and doing nothing illegal means you don’t have to worry.
- These threats underscore why proactive dark web monitoring is essential for cybersecurity teams.
Once you access the dark web, be mindful of potential security threats. Avoid clicking on suspicious links and be cautious about sharing personal information. Use reputable sources and forums for information, and always practice good cyber hygiene.
Understanding the Content of the Dark Web
The dark web hosts various types of content, some benign and others potentially harmful. Here are the main categories:
1. Legal Uses
- Whistleblowing: Platforms that enable whistleblowers to share sensitive information anonymously.
- Privacy Advocacy: Forums and communities focused on privacy, digital rights, and secure communication.
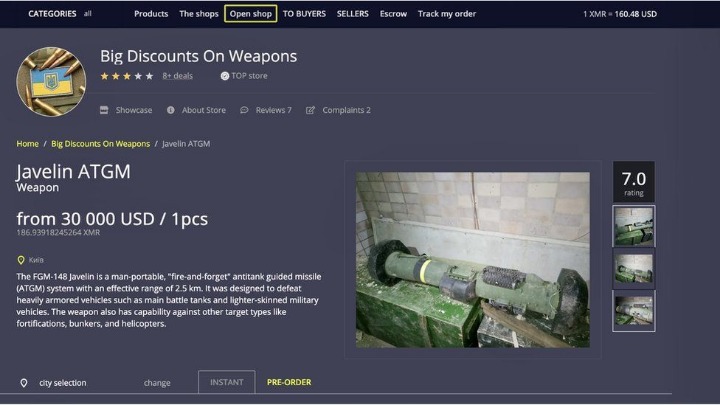
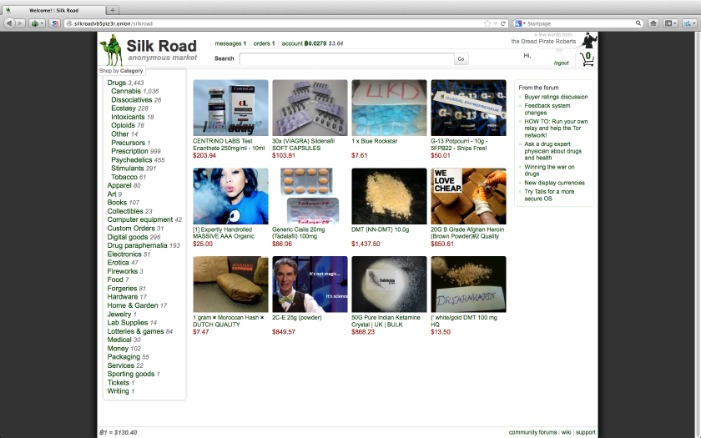
2. Illicit Activities
- Illegal Markets: Websites that facilitate the buying and selling of illegal goods and services.
- Hacking Services: Offerings to breach security systems and obtain data illegally.
Conclusion
While the dark web often gets a bad reputation due to its association with crime, it is crucial to understand its complexities. Knowing how to access the dark web safely can empower individuals to engage in protected communication and access information without fear of censorship. Those who venture into this obscure part of the internet should always prioritize their safety and be informed about the potential risks involved.