While it’s optional, using VPNs is crucial when trying to surf the dark web securely. Therefore, while accessing dark web links, it is crucial to exercise immense caution. In contrast to the deep web, safely accessing the dark web is not as easy. These three components make up the internet, which is available in our lives today.
Access to the dark web typically requires specialized software such as Tor, I2P, or Freenet, which encrypt traffic and route it through multiple nodes to anonymize user activity. While often linked to illicit activities, the dark web also hosts legitimate spaces for privacy, activism, and uncensored communication. Trends show increased interest in dark web access for research, journalism, and cybersecurity analysis, though users face risks like malware, scams, and legal repercussions. Ethical and technical safeguards are critical when studying this hidden network.
From cybersecurity and physical safety to risk management and emergency preparedness, we cover it all with a preventive mindset. There are many claims and rumors regarding the existence of red rooms on the dark web, but no credible evidence supports their existence as described in most of these stories. The dark web is a mysterious and often misunderstood part of the internet. Remember that no one can prevent all identity theft or cybercrime, and that LifeLock does not monitor all transactions at all businesses. To do that, you’ll need a dark web search engine like Torch or Ahmia. In some countries, like Russia or China, dark web access itself may be blocked or penalized.
The dark web, often shrouded in mystery and intrigue, is a part of the internet that isn't indexed by traditional search engines. While it can be associated with illegal activities, there are legitimate reasons people seek to gain access to the dark web. This article aims to shed light on the dark web's structure and uses, providing readers with essential information to help them navigate this hidden part of the internet safely and responsibly.
Access To The Dark Web
The dark web is a segment of the deep web, which encompasses all parts of the internet not indexed by standard search engines like Google or Bing. To understand how to gain access to the dark web, it's essential to recognize the tools and protocols involved.
Understanding the Structure
To access the dark web, users need specific software, most notably the Tor browser. Tor, which stands for "The Onion Router," enables users to browse the internet anonymously. By routing your connection through multiple servers, Tor masks your IP address, making it extremely difficult to track your online activities. This feature is the primary reason many individuals seek to gain access to the dark web.
Legitimate Uses of the Dark Web
While the dark web is often associated with illicit activities, it also offers various legitimate uses. Here are a few:
- Whistleblowing: Platforms like SecureDrop allows whistleblowers to share information with journalists while maintaining their anonymity.
- Privacy Protection: Individuals living under oppressive regimes often turn to the dark web to communicate securely and access information without fear of censorship.
- Research: Some researchers investigate the dark web to understand cybercrime trends, network security, and illicit trade practices.

Risks Involved
While there are legitimate reasons to gain access to the dark web, it's crucial to be aware of the inherent risks. The dark web can be a hotbed for scams, hacking attempts, and illegal activities. Users can accidentally find themselves in compromising situations or expose their personal information if they do not take adequate precautions. Here are some risks to consider:
- Malware: Downloading files from untrusted sources can lead to malware infections.
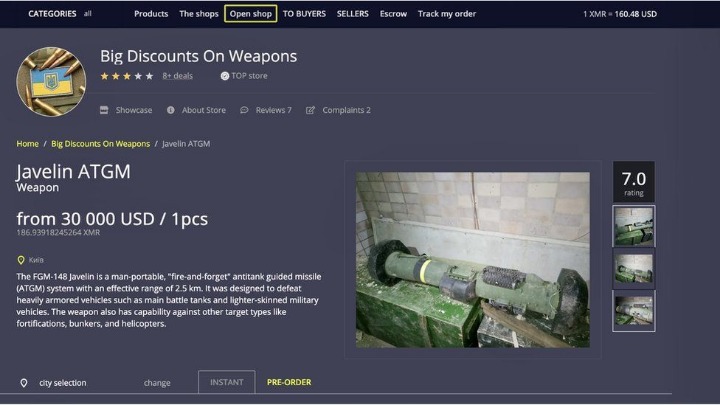
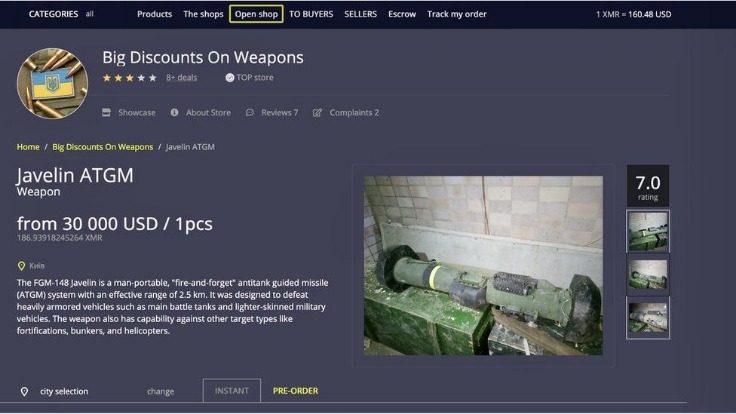
- Legal Consequences: Engaging with illegal services or materials can lead to severe legal repercussions.
- Privacy Issues: Misconfigured settings can expose a user’s location or identity.
- The standard dark web browser is Tor Browser, which directs your browser traffic through the Tor network so you can reach the darknet.
- Combined with smart surfing behaviour and technologies like Tor and a VPN, even the darkest reaches of the internet may be securely traversed.
- The dark web is rife with cybercriminals who offer their services either as individuals or as part of a group.
- Specialized search engines, directories, and wikis can help users locate the data they’re looking for.
- With its range of cybersecurity bundles, Surfshark is an excellent choice.
How to Access Safely
For those who still wish to explore the dark web for legitimate purposes, consider following these safety tips:
- Use a VPN: A Virtual Private Network adds an extra layer of anonymity, protecting your online activity.
- Keep Software Updated: Ensure that your Tor browser and operating system are up to date to protect against vulnerabilities.
- Avoid Personal Information: Never disclose personal information to maintain your anonymity.
Final Thoughts
Understanding how to gain access to the dark web responsibly is crucial in today's digital landscape. With the right tools and precautions, users can navigate this hidden segment of the internet for both legitimate research and privacy-centered activities. However, an awareness of the risks involved is essential to ensure a safe and informed experience.