Accessing the dark web requires specialized software, such as Tor, to anonymize internet traffic and bypass standard network protocols. It is a hidden portion of the internet where unindexed websites host a mix of legal and illegal content, including forums, marketplaces, and repositories of sensitive data. Users risk exposure to malware, scams, phishing attempts, and illicit activities. While some individuals use it for privacy, research, or circumventing censorship, law enforcement and cybersecurity experts warn of significant dangers, including identity theft and legal repercussions. Ethical and legal considerations are critical, as engagement with the dark web can inadvertently support criminal networks or violate security policies.
The dark web is often shrouded in mystery and misconceptions. While it is notorious for illegal activities, it also serves as a platform for privacy-conscious individuals and whistleblowers. Understanding how to access the dark web not only broadens internet users' knowledge but also highlights the importance of online safety and digital privacy. This guide provides a clear overview of the steps involved in accessing the dark web securely and responsibly.
Finding victims depicted in child sexual abuse materials is already a “needle in a haystack problem,” Rebecca Portnoff, the director of data science at the nonprofit child-safety group Thorn, told the Post. Certificate authorities may issue SSL certificates for HTTPS .onion sites per the process documented in the CA/Browser Forum's Baseline Requirements, introduced in Ballot 144. On 9 September 2015 ICANN, IANA and the IETF designated .onion as a 'special use domain', giving the domain an official status following a proposal from Jacob Appelbaum of the Tor Project and Facebook security engineer Alec Muffett. The purpose of using such a system is to make both the information provider and the person accessing the information more difficult to trace, whether by one another, by an intermediate network host, or by an outsider. The "onion" name refers to onion routing, the technique used by Tor to achieve a degree of anonymity.
Access The Dark Web
- The group describes itself as a “politically neutral underground syndicate” focused solely on financial gain, with examples of demands such as “a sudden tax on your security negligence”.
- The many layers of an onion represent the multiple layers of encryption in the Tor network.
- Like the regular surface web, the dark web offers its own social media sites and web forums.
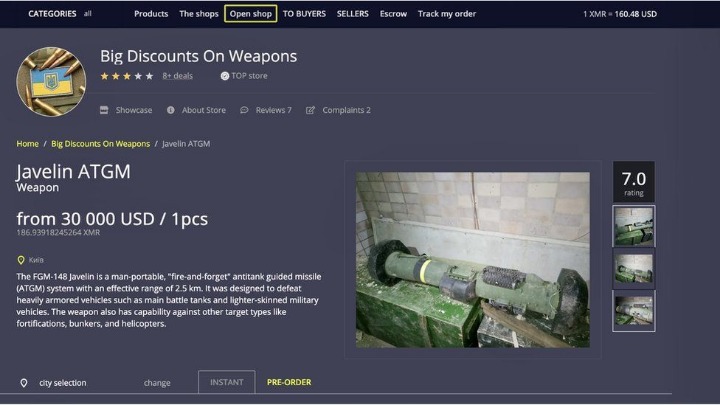
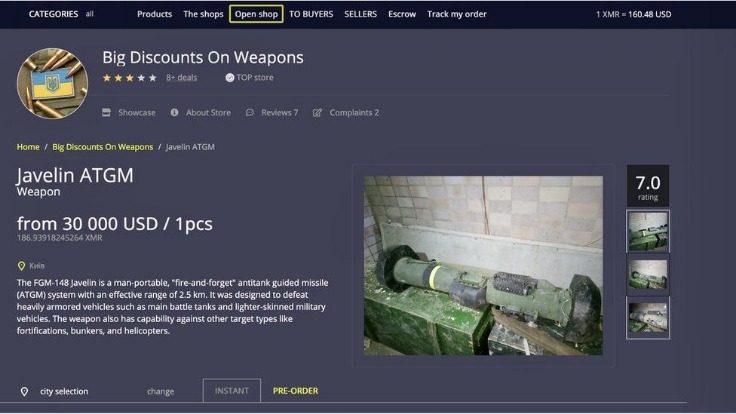
- Mostly on the dark web, financial transactions happen via cryptocurrencies such as Bitcoin, making it possible for parties to do business anonymously.
- Given the associations that the dark web has and some of the illegal activities that take place on it, you won't find a huge number of well-known websites on there—a lot of the dark web is made up of sites, wikis, and forums maintained by volunteers.
- Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent.
What You Need to Access the Dark Web

Before diving into the dark web, it's essential to prepare adequately. Here are the basic requirements:
- Secure Internet Connection: Use a reliable and secure connection to protect your data.
- VPN (Virtual Private Network): A VPN adds an extra layer of security by masking your IP address.
- Tor Browser: The primary tool for accessing the dark web. It anonymizes your internet traffic.
- Antivirus Software: Ensure your device is protected against malware that might be present on unregulated sites.
Steps to Access the Dark Web
To safely navigate the dark web, follow these steps:
- Install a VPN: Connect to a trusted VPN service to enhance your privacy.
- Download Tor Browser: Visit the official Tor Project website to download the Tor Browser.
- Install Tor Browser: Follow the installation prompts and launch the browser.
- Connect to Tor: Open the Tor Browser and connect, which will route your traffic through multiple nodes for anonymity.
- Access .onion sites: Use known .onion web addresses to explore dark web content. Be cautious and research sites before visiting.
Safety Tips While Browsing the Dark Web
Safety should be your priority when exploring the dark web. Remember the following tips:
- Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations.
- As data breaches, mass surveillance, and online tracking become increasingly common, understanding how the Dark Web works and how to access it safely has never been more relevant.
- Some websites monitor and analyze the dark web for threat intelligence.
- Initially designed for secure military communications, it evolved into a broader tool for online anonymity, later expanding to public use with the Tor network.
- The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web).
- Avoid Sharing Personal Information: Never disclose your identity or sensitive information.
- Be Wary of Downloads: Files from untrustworthy sources may contain harmful software.
- Stay Updated on Security Practices: Follow the latest advice on cybersecurity to stay protected.
- Engage with Caution: Interactions on the dark web can expose you to potential risks.
FAQs About Accessing the Dark Web
Is the dark web illegal?
Accessing the dark web itself is not illegal; however, many activities conducted there may be against the law. Always prioritize legal and ethical practices.
Can I be traced while using the dark web?
While tools like Tor provide anonymity, no browsing method is entirely foolproof. Using a VPN alongside Tor minimizes the risk of being traced.
What types of content can I find on the dark web?
The dark web hosts various content, including forums, blogs, and marketplaces. Not all are illicit; some focus on political activism, privacy protection, and information sharing.
Is it safe to explore the dark web?
While there are safe spaces on the dark web, many areas can be hazardous. It is crucial to observe stringent security measures and remain vigilant.
Understanding how to access the dark web equips users with knowledge about the hidden corners of the internet. By following the steps and safety tips highlighted in this guide, individuals can explore responsibly, ensuring both security and awareness in this digital landscape.